Virtualization has revolutionized the way businesses handle their IT infrastructure, offering flexibility and efficiency that wasn’t possible in the past. But like any technology, it has its advantages and drawbacks. Let’s take a closer look at the pros and cons of virtualization to see how it might fit into your business strategy.
Read MoreEvery business fears cyberattacks. With so much of our modern world going online, a cyberattack has gone from a nuisance to a massive problem. You need to understand what goes into one—and how it can affect you.
Read MoreThe cloud is more than just your Google Drive or your online applications. It’s a powerful tool you can use to supercharge your servers—and here’s why.
Read MorePhishing is one of the most common cyberattacks you’ll encounter. It’s a simple concept: someone pretends to be someone they’re not by spoofing a website or an email. They ask for personal information, then steal that information.
Read MoreRemote work has taken over the white-collar world. 58% of Americans surveyed by McKinsey had the opportunity to work from home at least one day a week in 2022. The workforce has changed, and working from home is now commonplace.
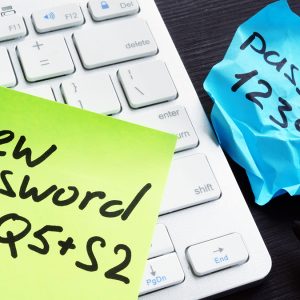
Read MoreWorkstation login. Cloud login. Email login. A hundred different application logins. Modern business requires a lot of passwords! It can be daunting to keep up and easy to start taking shortcuts with your security.
Read MoreThere’s a difference between home- and commercial-grade tools. It’s essentially common sense that the drill you use to put up the curtains in your house won’t stand up to being thrown in and out of toolboxes and used eight hours a day on a job site.
Read MoreCybersecurity used to be something of an afterthought. But in today’s hyper-connected world, it’s an everyday concern. The average person probably knows about ransomware, phishing, and social engineering.
Read MoreSmall businesses need technology and connectivity to survive in the modern world. And if you’re looking to upgrade, it can be challenging to figure out what’s important. If you’ve been confused by the number of server options out there, you’re not alone.
Read MoreSome employees have headed back to the workplace, but remote work is entrenched now, and many companies are allowing either fully remote or hybrid employment. That means a new set of challenges for organizations.
Read More